
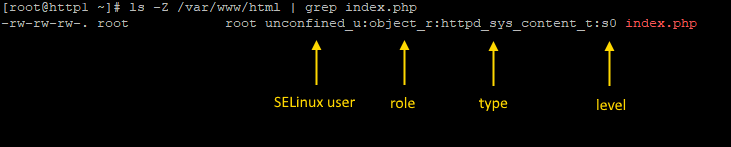
The ls command with the -Z flag can be used to view the SELinux context of a file or directory.
~]# ls -Z /var/www/html
-rw-r--r--. root root unconfined_u:object_r:httpd_sys_content_t:s0 index.php
The Selinux context has 4 parts - SELinux user : role : type : level.
Confined / Targeted
When SELinux is enforcing and targeted, SELinux will check a files context, and then do something based on the context. The sestatus command can be used to determine if SELinux is enforcing and targeted.
~]# sestatus
Loaded policy name: targeted
Current mode: enforcing
Nearly every network service, such as HTTP and SSH, are confined by SELinux. Similarly, many of the commands in the sbin directory are confined by SELinux.
When SELinux is enforcing and targeted, certain files will need a certain SELinux type. For example, if index.php does not have type httpd_sys_content_t, the web server should not be able to send the index.php file to the client, and the web browser should display some error, such as page not found. On the other hand, if index.php has type httpd_sys_content_u, the web browser should be able to send index.php to the client.
When using SELinux, it is important to ensure files have an appropriate context.
SELinux user
It is noteworthy that there is a relationship between the SELinux user and the normal Linux user account. The semanage command can be used to see the mapping. In the example, user John Doe is mapped to unconfined_u.
~]# semanage login -l
Login name SELinux user
john.doe unconfined_u
Create new directory
When a new directory is created, the default SELinux context of the directory is determined by the rules of the /etc/selinux/targeted/contexts/files/file_contexts files. For example, when the /home/JohnDoe/.ssh directory is created, the directory will have ssh_home_t context.
~]# mkdir /home/JohnDoe/.ssh
~]# ls -Z /home/JohnDoe
drwxrwxr-x. JohnDoe JohnDoe unconfined_u:object_r:ssh_home_t:s0 .ssh
The context of the .ssh directory is ssh_home_t because the /etc/selinux/targeted/contexts/files/file_contexts.homedirs file contain the following rule, which sets the .ssh directory to ssh_home_t.
/home/[^/]+/\.ssh(/.*)? unconfined_t:object_r:ssh_home_t:s0
Create new file
When a new file is created, the file will inherit the SELinux type of the parent directory. For example, if the /srv/samba/share directory has type samba_share_t, files created in the /srv/samba/share directory will also have type samba_share_t.
Copy or move file
Problems can occur when copying or moving files. For example, a file created in the /etc directory will probably have type etc_t. If the file is copied or moved to /srv/samba/share, the file may retain type etc_t. SELinux will detect that the file does not have the appropriate type for Samba. When attempting to interact with the file, some error will be displayed. There are a few ways to address this challenge.
Did you find this article helpful?
If so, consider buying me a coffee over at 