
By default, security auditing is not enabled in WebSphere. In the left panel of the WebSphere web console, expand Security and select Security auditing. Check Enable security auditing and select Apply.
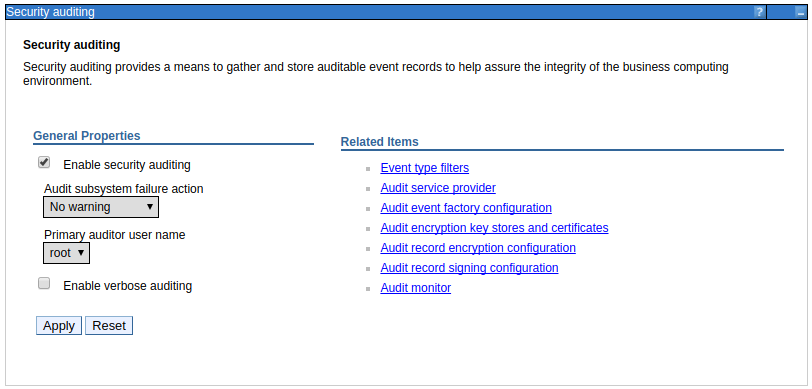
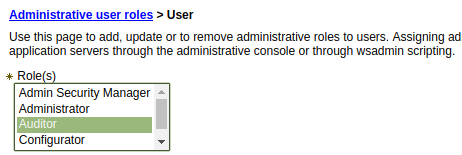
By default, only the primary administrative user is allowed to modify security auditing. In the screen shot above, the primary administrative user is root. To allow other users to be able to modify security auditing, the other users will need to have the Auditor administrative role.
This will create a file named BinaryAudit_cellName_cellManager_dmgr.log files in the /opt/IBM/WebSphere/your_server/profiles/your_profile/logs/dmgr/ directory.
As the name implies, security auditing will log security related events. For example, let's say you provide an invalid username and password when attempting to sign into the deployment manager web console.
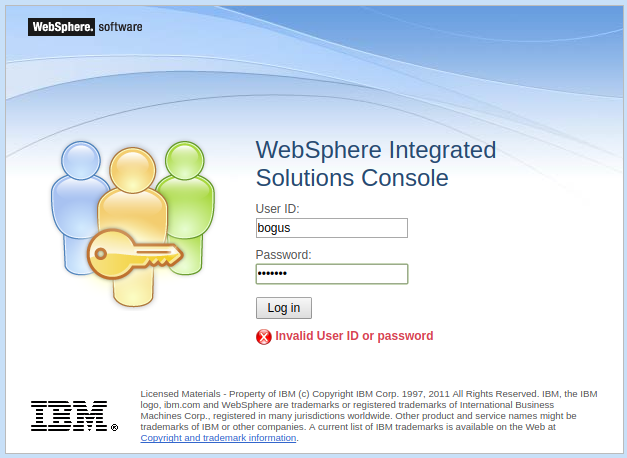
In this scenario, there will be a record in the BinaryAudit_cellName_cellManager_dmgr.log file.
Seq = 731 | Event Type = SECURITY_AUTHN | Outcome = UNSUCCESSFUL | OutcomeReason = DENIED
OutcomeReasonCode = 15 | SessionId = XsjvDfivWj_fuFnfSvis | RemoteHost = 10.4.56.223
RemoteAddr = 10.4.56.223 | RemotePort = 56384 | ProgName = /j_security_check
Action = webAuth | AppUserName = bogus | ResourceName = POST | RegistryUserName = bogus
AccessDecision = denied | ResourceType = web | ResourceUniqueId = 0 | PermissionChecked = null
PermissionGranded = null | RolesChecked = null | RolesGranted = null . . .
Configuring the events in the log
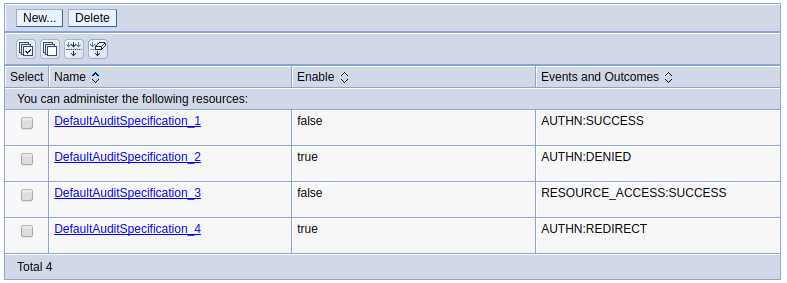
The type of events in the security log can be configured.
- In the WebSphere admin console, expand Security and select Security auditing.
- Select Event type filters.
- Select a filter to modify. The default filters can be enabled or displayed, and the log level (info warning error denied failure success challenge redirect) can be added or removed.
In this example, the default SECURITY_AUTHN SUCCESS records are disabled (by removing the check from the Enable check box).
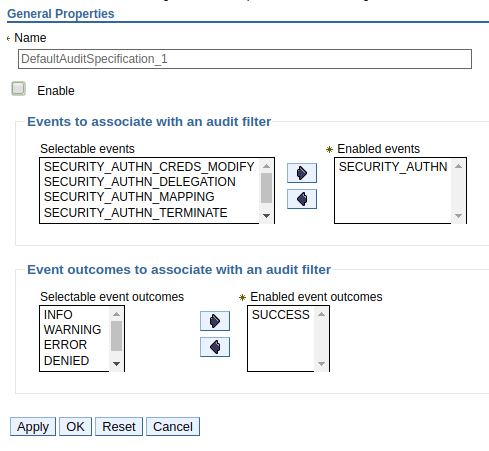
In this example, two of the default filters are disabled (set to false).
Did you find this article helpful?
If so, consider buying me a coffee over at 