
If you are not familar with firewalld and the firewall-cmd, check out our Getting Started article.
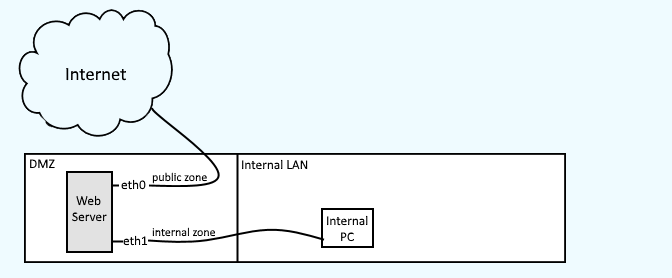
Firewalld uses zones, such as public, internal, and dmz. Each zone has its own unique set of rules. For example, public zone can be bound to eth0 and only allow HTTP, and internal zone can be bound to eth1 and allow both HTTP and SSH.
The firewall-cmd --list-all-zones command can be used to show all of the zones.
firewall-cmd --list-all-zones
Which should return something like this.
internal
target: default
icmp-block-inversion: no
interfaces:
sources:
services: dhcpv6-client mdns samba-client ssh
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
public (active)
target: default
icmp-block-inversion: no
interfaces: eno16780032
sources:
services: dhcpv6-client ssh
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
trusted
target: ACCEPT
icmp-block-inversion: no
interfaces:
sources:
services:
ports:
protocols:
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
One of the most useful commands is firewall-cmd --list-all. If a zone is not specified, the default zone will be displayed. In this example, public is the default zone.
~]# firewall-cmd --list-all
public
target: default
icmp-block-inversion: no
interfaces: eth0
sources:
services: https
ports:
protocols:
masquerade: no
forward-ports:
sourceports:
icmp-blocks:
rich rules:
The --zone=zone_name option can be used to display the settings for a specific zone.
~]# firewall-cmd --list-all --zone=internal
. . .
Information about each zone will be listed in an .xml file at /usr/lib/firewalld/zones/ or /etc/firewalld/zones/. The files in the /usr/lib/firewalld/zones/ should not be edited. When a change is made to a zone, the .xml file will be copied from /usr/lib/firewalld/zones/ to /etc/firewalld/zones/. The .xml files at /etc/firewalld/zones/ can be edited. If the /etc/firewalld/zones/ directory does not contain a file for a zone, this means no changes have been made to the zone.
The default zone can be changed using the --set-default-zone=zone_name option. In this example, the default zone is set to DMZ.
~]$ firewall-cmd --set-default-zone=dmz
Or, add DefaultZone=zone_name to /etc/firewalld/firewalld.conf.
DefaultZone=dmz
Or, you can add ZONE=zone_name to the /etc/sysconfig/network-scripts/ifcfg-xxxxxxx file.
ZONE=public
Instead of using --list-all, you can instead list a single item.
- --list-ports
- --list-protocols
- --info-service=service_name
- --query-masquerade
Did you find this article helpful?
If so, consider buying me a coffee over at 