
SAML is the abbreviation for Security Assertion Markup Language and is an open source authentication and authorization system created by OASIS. The most venerable authentication system is basic authentication, which is providing a username and password to get authenticated and authorized. Basic authentication has these drawbacks:
- Users must sign into each unique system
- Users must reset their password often
- Users must use a strong password
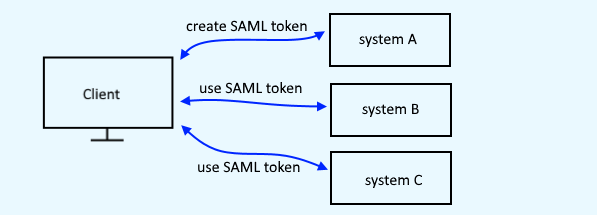
SAML resolves some of these issues. With SAML, a user signs into one system and a SAML token is created. Then, as the user navigate to other systems, if the other system is part of the SAML hierarchy, the user is authenticated and authorized into the system via the SAML token. In this way, the user does not need to sign into each system in the SAML hierarchy. Instead, the user sign into system "a" and then is granted access to systems "b", "c", "d", et cetera.
Users Repository (LDAP)
SAML is not the system that is used to maintain user accounts (username, password, et cetera). Instead, some other system, such as LDAP or Active Directory, is used to maintain user accounts. For the sake of this tutorial, let's say you have an user accounts system setup with a user account for John Doe.
Identity Provider (IdP)
At it's core, a SAML heirarchy is made up of two pieces, the Identity Provider (IdP) and the Service Provider (SP). The Identity Provider is the system that validates a users identity. For example, the IdP would validate that John Doe is a valid user in the user accounts system (LDAP, Active Directory, et cetera).
Service Provider (SP)
The service provider is the part of SAML that is used to provide SAML authentication against something, most usually an HTTPS web page. For example, let's say www.example.com/secure is your current basic authentication page. The SP should be able to be configured so that www.example.com/secure can be authenticated via SAML.
Did you find this article helpful?
If so, consider buying me a coffee over at 