
GitHub Actions can be used to do something whenever something happens in one of your GitHub repositories. If you are not familiar with GitHub Actions, check out my article Getting Started with GitHub Actions.
For example, let's say you have a repository named my-repo that contains files that you store in an Amazon Web Services (AWS) S3 Bucket. For example, perhaps your my-repo repository contains two JPGs, foo.jpg and bar.jpg, perhaps like this.
- https://github.com/JohnDoe/my-repo/blob/main/images/foo.jpg
- https://github.com/JohnDoe/my-repo/blob/main/images/bar.jpg
For example, your GitHub Action YAML could have something like this. Notice in this example that the AWS access key and secret key are stored in GitHub Secrets. In your repository, you would go to Settings > Secrets and variables > Actions and create the AWS_KEY_ID and AWS_SECRET_ACCESS_KEY secrets.
name: GitHub Action
run-name: ${{ github.workflow }} run by ${{ github.actor }}
on:
push:
branches:
- main
jobs:
github-action-job:
runs-on: ubuntu-latest
steps:
- name: Checking out the repository code . . .
uses: actions/checkout@v4
- name: upload images to S3 Bucket my-bucket-abcdefg
uses: shallwefootball/s3-upload-action@master
id: S3
with:
aws_key_id: ${{ secrets.AWS_KEY_ID }}
aws_secret_access_key: ${{ secrets.AWS_SECRET_ACCESS_KEY }}
aws_bucket: my-bucket-abcdefg
source_dir: images
destination_dir: images
You may also need to update your S3 bucket so that public ACLs are not blocked, otherwise you may get "AccessControlListNotSupported The bucket does not allow ACLs"
The aws s3api get-public-access-block command can be used to see if the S3 Bucket had Public Access blocked.
~]$ aws s3api get-public-access-block --bucket my-bucket-abcdefg
{
"PublicAccessBlockConfiguration": {
"BlockPublicAcls": true,
"IgnorePublicAcls": true,
"BlockPublicPolicy": true,
"RestrictPublicBuckets": true
}
}
If it does, the aws s3api delete-public-access-block command can be used to remove the public access block.
aws s3api delete-public-access-block --bucket my-bucket-abcdefg
And then the aws s3api put-public-access-block command to set BlockPublicAcls=false and the others to true.
aws s3api put-public-access-block \
--bucket my-bucket-abcdefg \
--public-access-block-configuration "BlockPublicAcls=false,IgnorePublicAcls=true,BlockPublicPolicy=true,RestrictPublicBuckets=true"
And confirm BlockPublicAcls is now set to false.
]$ aws s3api get-public-access-block --bucket my-bucket-abcdefg
{
"PublicAccessBlockConfiguration": {
"BlockPublicAcls": false,
"IgnorePublicAcls": true,
"BlockPublicPolicy": true,
"RestrictPublicBuckets": true
}
}
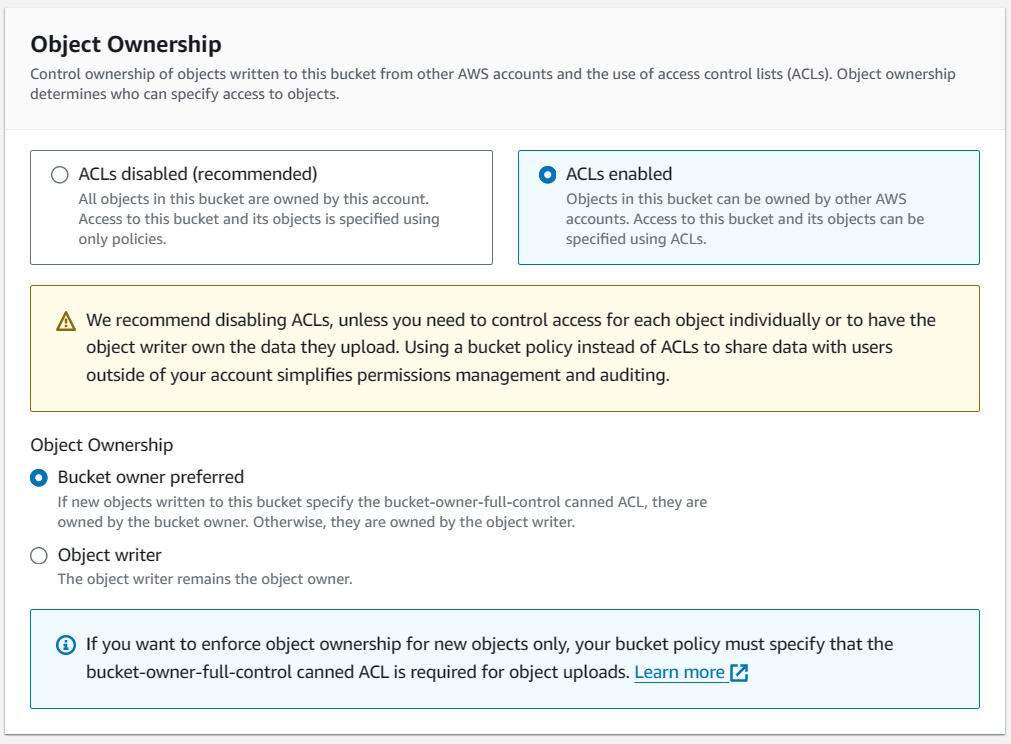
You may also need to update Object Ownership to ACLs enabled.
Did you find this article helpful?
If so, consider buying me a coffee over at 