
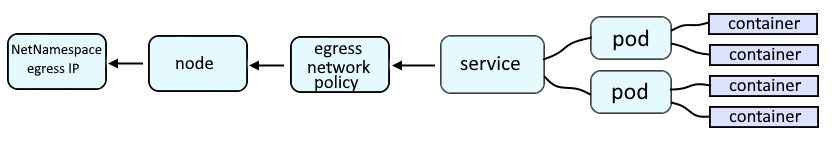
Egress provides a way for an application deployed on OpenShift to access an external URL, such as http://www.example.com.
Optionally, NetNamespace is used to assign an egress IP address to one or more namespaces, so that all egress traffic from the namespace is using a dedicated IP address. By assigning a specific egress IP address to a namespace, all outbound (egress) requests from applications in the project will come from the dedicated egress IP address, making it easier to find the requests that came from applications in the project. This also makes it possible to have two (or more) different projects share the same egress IP address, as a way to group similar projects together.
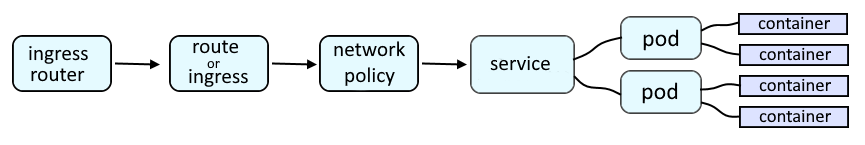
An OpenShift route or an Ingress route will provide a URL such as http://route001-project001.apps.openshift.example.com:8080 which is used to route a request onto a service, which is then routed onto a pod, and then to the container in the pod, and finally to the application running in the container.
If you are not familiar with the oc command, refer to OpenShift - Getting Started with the oc command.
The oc get egressnetworkpolicy command can be used to list the egress rules in your currently selected project / namespace. In this example, no egress rules have been created.
TIP
The -A or --all-namespaces flag can be used to list the egress network policies in every project / namespace.
The -n or --namespace flag can be used to list the egress network policy in a certain project / namespace.
~]$ oc get egressnetworkpolicy
No resources found in default namespace.
In this example, there is an egress network policy named egress-traffic.
~]$ oc get egressnetworkpolicy --namespace foo
NAME AGE
egress-traffic 630d
The -A or --all-namespaces command can be used to list the egress network policies in each project / namespace.
~]$ oc get egressnetworkpolicy --all-namespaces
NAMESPACE NAME AGE
project001 egress-traffic 543d
project002 egress-traffic 650d
project003 egress-traffic 650d
The oc describe egressnetworkpolicy command can be used to display egress related configuration. In this example, the egress settings for the project/namespace named foo is displayed. The rules are read in order, which means the deny rule should always be the very last rule.
~]$ oc describe egressnetworkpolicy egress-traffic --namespace foo
Name: egress-traffic
Namespace: project001
Created: 10 months ago
Labels: <none>
Annotations: <none>
Rule: Allow to 10.7.19.24
Rule: Deny to 0.0.0.0/0
Or, the oc get egressnetworkpolicy command with the --output json or --output yaml option can be used.
~]$ oc get egressnetworkpolicy egress-traffic --output json
{
"apiVersion": "network.openshift.io/v1",
"kind": "EgressNetworkPolicy",
"metadata": {
"creationTimestamp": "2022-01-05T14:56:39Z",
"generation": 26,
"managedFields": [
{
"apiVersion": "network.openshift.io/v1",
"fieldsType": "FieldsV1",
"fieldsV1": {
"f:spec": {
".": {},
"f:egress": {}
}
},
"manager": "HashiCorp",
"operation": "Update",
"time": "2022-01-05T14:56:39Z"
}
],
"name": "egress-traffic",
"namespace": "enterprise-services",
"resourceVersion": "979952915",
"uid": "07519a24-ad2d-4f6f-89b9-5d30aab6bf9f"
},
"spec": {
"egress": [
{
"to": {
"cidrSelector": "10.7.19.0/24"
},
"type": "Allow"
},
{
"to": {
"cidrSelector": "0.0.0.0/0"
},
"type": "Deny"
}
]
}
}
The --output jsonpath option can be used to print the value of a specific JSON key.
~]$ oc get egressnetworkpolicy egress-traffic --output jsonpath={.spec.egress[*].to.cidrSelector}
10.87.188.21/32 0.0.0.0/0
Did you find this article helpful?
If so, consider buying me a coffee over at 