
If you are not familiar with the oc command, refer to OpenShift - Getting Started with the oc command.
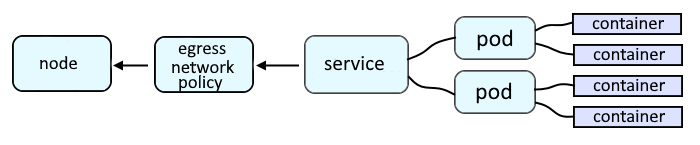
Egress provides a way for an application deployed on OpenShift to access an external URL, such as http://www.example.com.
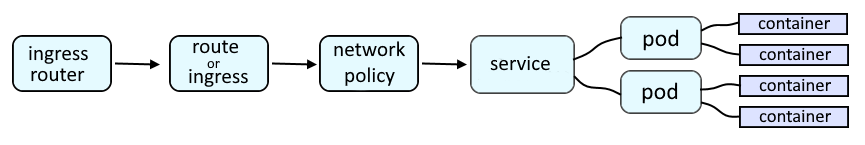
An OpenShift route or an Ingress route will provide a URL such as http://route001-project001.apps.openshift.example.com:8080 which is used to route a request onto a service, which is then routed onto a pod, and then to the container in the pod, and finally to the application running in the container.
The oc get networkpolicies command can then be used to list the network policies that have been created in the project / namespace.
TIP
The -A or --all-namespaces flag can be used to list the network policies in every project / namespace.
The -n or --namespace flag can be used to list the network policies in a certain project / namespace.
~]$ oc get networkpolicies
NAME POD-SELECTOR AGE
allow-ingress-region-east region=east 41s
Following are the common types of Network Policies.
- Allow or deny all requests coming in (ingress) to a project / namespace
- Allow or deny all requests going out (egress) of a project / namespace
- Allow or deny requests coming in (ingress) to a project / namespace from some other project / namespace
- Allow or deny requests coming in (ingress) to a project / namespace that do not match a pods label (e.g. region=east)
- Allow or deny requests coming in (ingress) to a project / namespace from an IP address outside of a certain IP subnet (e.g. 172.17.0.0/16)
- Allow or deny requests going out (egress) of a project / namespace to an IP subnet (e.g. 10.0.0.0/24) and a specific Port (e.g. 8080) or a Port range (e.g. 30000 - 31000)
The oc describe networkpolicy command can be used to show more detail about a network policy.
~]$ oc describe networkpolicy allow-ingress-region-east
Name: allow-ingress-region-east
Namespace: default
Created on: 2022-08-29 20:43:23 -0500 CDT
Labels: <none>
Annotations: <none>
Spec:
PodSelector: region=east
Allowing ingress traffic:
To Port: <any> (traffic allowed to all ports)
From:
PodSelector: access-to-service=true
Not affecting egress traffic
Policy Types: Ingress
Or, the oc get networkpolicy command with the --output json or --output yaml option can be used.
~]$ oc get networkpolicy allow-ingress-region-east --output yaml
apiVersion: networking.k8s.io/v1
kind: NetworkPolicy
metadata:
creationTimestamp: "2022-08-30T01:43:23Z"
generation: 1
name: allow-ingress-region-east
namespace: foo
resourceVersion: "478694700"
uid: 279bf32b-a838-4dd6-9d41-774a28876696
spec:
ingress:
- from:
- podSelector:
matchLabels:
access-to-service: "true"
podSelector:
matchLabels:
region: east
policyTypes:
- Ingress
Did you find this article helpful?
If so, consider buying me a coffee over at 