
If you are not familiar with the oc command, refer to OpenShift - Getting Started with the oc command.
There are different ways to configure a container with environment variables.
- In a deployment YAML file
- Using Config Map
- Using Secrets (this article)
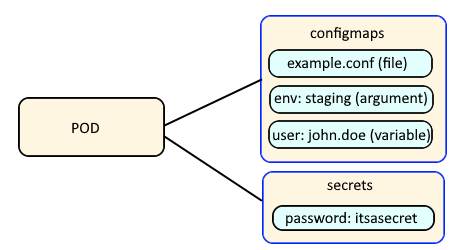
Config Maps are used to:
- mount configuration files in a container
- create environment variables in a container
- create command line option arguments in a container
Secrets are similar, used to create variables that contain encoded data (e.g. passwords). In this way, if a change is needed to a configuration file, variable, or command line option argument, you just need to update the config map or secret as opposed to having to make the change to your applications or deployments.
The oc get secret command can be used to list the secrets that have been created in the currently selected project / namespace.
~]# oc get secrets
NAME TYPE DATA AGE
my-secret Opaque 1 133d
The --output yaml or --output json options can be used to display the YAML or JSON details of the secret. Notice that the "foo" key contains "SGVsbG8=" and "bar" contains "V29ybGQ=". This is normal, because the secret value is base64 encoded.
~]$ oc get secrets my-secret --output yaml
apiVersion: v1
data:
bar: V29ybGQ=
foo: SGVsbG8=
kind: Secret
metadata:
creationTimestamp: "2021-11-18T07:12:09Z"
name: mysecret
namespace: default
resourceVersion: "448072461"
uid: 4104a646-84e2-46c3-bd59-408e2f7ee807
type: Opaque
On a Linux system, the base64 command can be used to decode the value.
~]# echo SGVsbG8= | base64 --decode
Hello
~]# echo V29ybGQ= | base64 --decode
World
Let's say you have a deployment named "my-deployment".
~]# oc get deployments
NAME READY UP-TO-DATE AVAILABLE AGE
my-deployment 1/1 1 1 8d
There are two ways to update the deployment to use the foo and bar secrets in my-secret.
- Using the oc edit command
- Using the oc set env command
The oc edit command can be used to edit the deployment.
oc edit deployment my-deployment
A secret can be made available to a container:
- As a variable (this article)
- As a volume mount
Here is an example of what you would have in the deployment YAML to use the value in the "foo" and "bar" keys in the secret named "my-secret".
apiVersion: v1
kind: Deployment
spec:
template:
spec:
containers:
- env:
- name: foo-secret <- this will be the variable name/key in the container
valueFrom:
secretKeyRef:
key: foo <- must match the key in the secret
name: my-secret <- must match the secret name
- name: bar-secret <- this will be the variable name/key in the container
valueFrom:
secretKeyRef:
key: bar <- must match the key in the secret
name: my-secret <- must match the secret name
- image: api.openshift.example.com/myapp
name: my-app
Or, envFrom can be used instead of env. With this approach, all of the variables (key/values) in the secret will be available in the container.
apiVersion: v1
kind: Deployment
spec:
template:
spec:
containers:
- envFrom:
- secretRef:
name: my-secret <- must match secret name
Or, the oc set env command can be used.
~]$ oc set env deployment my-deployment --from secret/my-secret
deployment.apps/my-deployment updated
A new pod should immediately be created after the oc edit or oc set env commands have been completed, and the oc describe pod command can be used to see that the pod is now has the "foo" and "bar" keys.
~]$ oc describe pod my-pod-65rbl
Containers:
my-container:
Container ID: my-image
Image ID: my-image
Ports: 8080/TCP, 8443/TCP
Host Ports: 0/TCP, 0/TCP
State: Running
Started: Tue, 02 Aug 2022 06:28:49 -0500
Ready: True
Restart Count: 0
Environment:
foo-secret: <set to the key 'foo' in secret 'my-secret'> Optional: false
bar-secret: <set to the key 'bar' in secret 'my-secret'> Optional: false
my-environment-variable: Hello World
The oc set env command with the --list option can be used the list the environment variables associate with a resource, such as a deployment or pod.
~]$ oc set env pod my-pod-276pc --list
# pods/my-pod-276pc, container my-container
# FOO from secret my-secret, key foo
# BAR from secret my-secret, key bar
my-environment-variable=Hello World
The oc exec command and the env or printenv command can be used to see if the "foo-secret" variable contains a value of "Hello" in the container.
~]$ oc exec/my-pod-65rbl -- env
foo-secret=Hello
bar-secret=World
Did you find this article helpful?
If so, consider buying me a coffee over at 