
If you are not familiar with the oc command, refer to OpenShift - Getting Started with the oc command.
Role Bindings are a way to map subjects (user, group, service account) to a Role or Cluster Role, so that the subjects have permission to perform certain actions (e.g. create, delete) on certain resources (e.g. deployments, secrets). In other words, Role Bindings are a way to apply Role Based Access Control (RBAC). Here is an illustration of how subjects (user, group, service account) get mapped to permissions. There are a number of different ways to design this, typically based on your organizations needs.
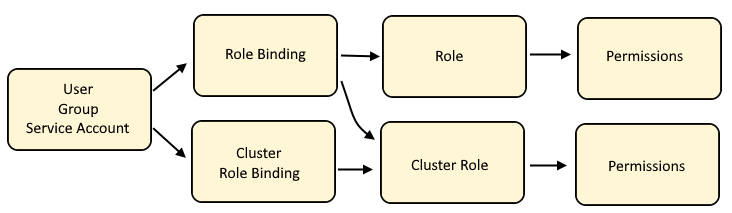
Cluster Role Binding maps a user, group or service account to a Cluster Role which will have policies that allow certain actions (such as create or delete or list) on certain resources (such as deployments, pods)
Role Bindings maps a user, group or service account to a Role or to a Cluster Role which will have policies that allow certain actions (such as create or delete or list) on certain resources (such as deployments, pods)
Cluster Role is often used by a number of different users, groups and service accounts in various projects, thus a Cluster Role contains the default actions (such as list, get, watch) on certain resources (such as deployments, pods) that users, groups, or service accounts are allowed to do across namespaces.
Role if isolated to a user, group or service account in a specific project, as a way of granting specific actions (such as create and delete and update) on certain resources (such as services and routes).
Role's include verbs, which are the actions that the role allows.
- create
- delete
- get
- list
- patch
- update
- watch
Role's also include API Groups, which are the API Groups that the role is allowed. Often, Roles are allowed in all API Groups (wildcard). However, role's can be limited to certain API groups, such as "apps/v1" which would only allow the Role to do an actions on resources in the "apps/v1" API Group.
And roles are applied to resources. For example, following are some of the more common resources.
- configmap
- deployment
- namespace
- pod
- project
- route
- secret
- service
The oc get roles command can be used to list the roles that have been created in your currently selected project.
~]$ oc get roles
NAME CREATED AT
my-role 2023-01-05T08:19:22Z
Or in the OpenShift console at User Management > Roles.
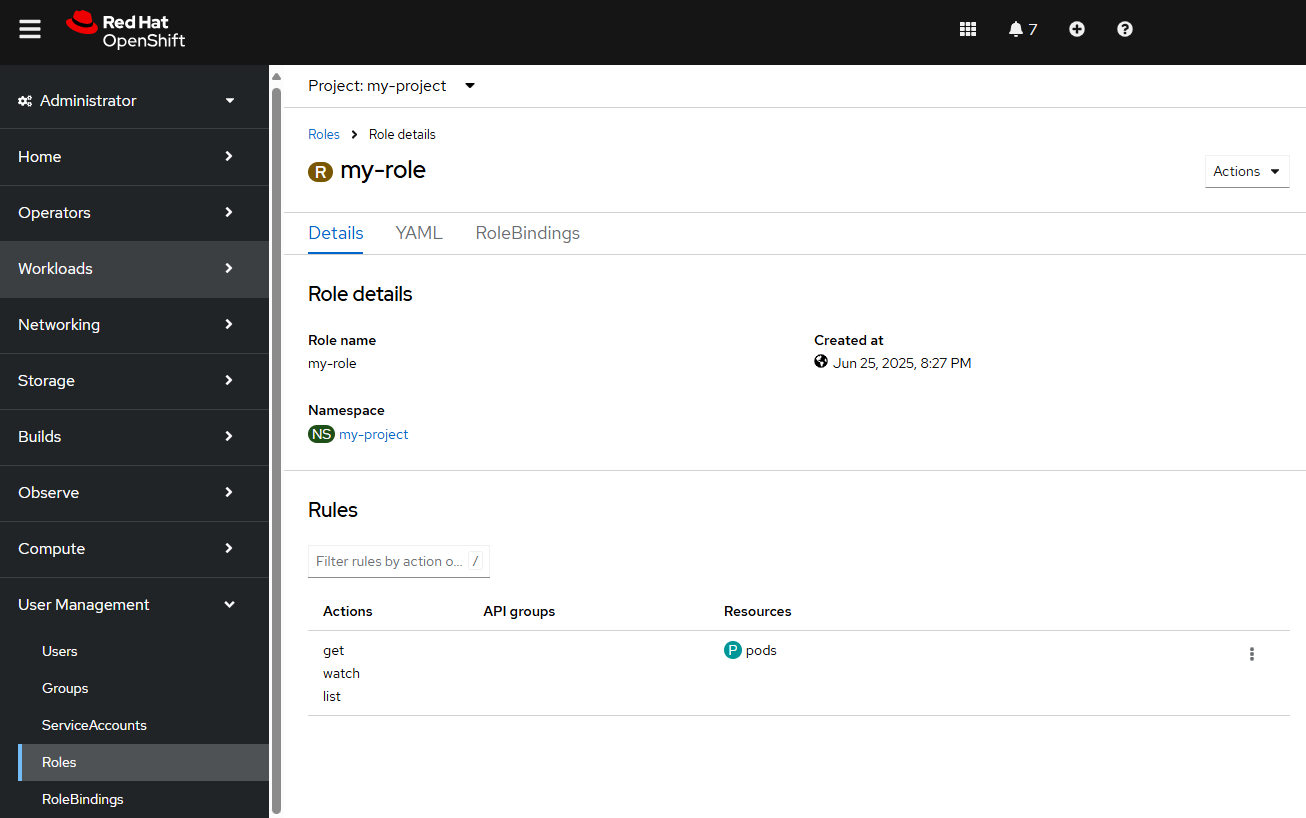
The oc get clusterroles command can be used to list the roles that are automatically included with OpenShift and any additional Cluster Roles that you have created.
~]$ oc get clusterroles
NAME CREATED AT
admin 2021-07-16T17:15:10Z
my-cluster-role 2023-01-05T08:19:22Z
basic-user 2021-07-16T17:15:10Z
cluster-admin 2021-07-16T17:15:10Z
cluster-reader 2021-07-16T17:15:10Z
cluster-status 2021-07-16T17:15:10Z
edit 2021-07-16T17:15:10Z
self-provisioner 2021-07-16T17:15:10Z
view 2021-07-16T17:15:10Z
Or in the OpenShift console at User Management > Roles.
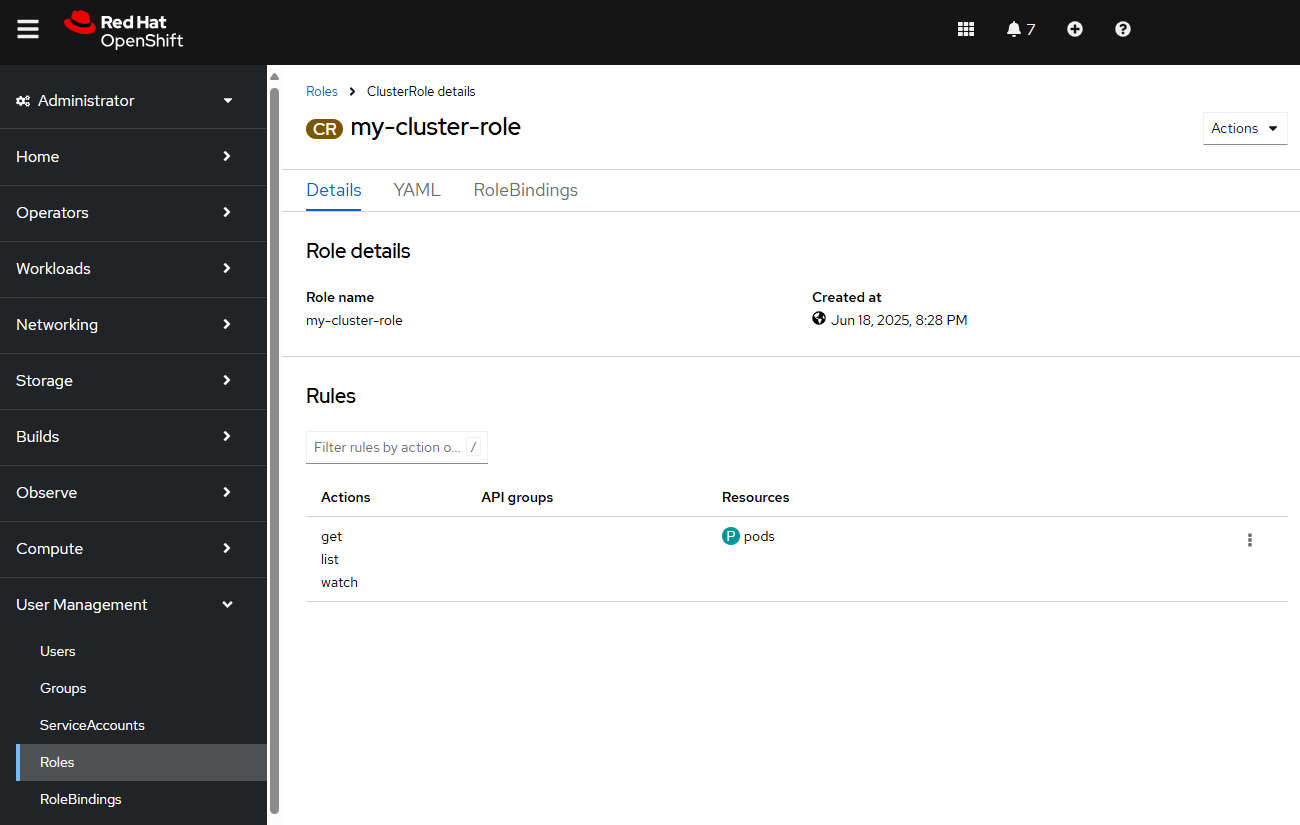
By default, an OpenShift cluster should include the following Cluster Roles.
| Cluster Role | Description |
| admin | Allowed to view and edit/modify all resources except for quota |
| basic-user | no access to projects or resources (i'm not sure why you would ever want to apply this role to a user) |
| cluster-admin | full control |
| cluster-status | view basic cluster status information |
| cluster-reader | allowed to view, but cannot edit or modify |
| edit | allowed to view and edit certain resources such as deployments/pods/services/routes but not allowed to view or edit resources such as role bindings |
| self-provisioner | user can create their own projects |
| view | allowed to view resources, but cannot edit or modify resources |
Create a Role or Cluster Role
Check out my article FreeKB - OpenShift - Create Roles.
Determine if a User, Group or Service Account has permission to perform an action on a resource
Check out my article Determine if a User, Group or Service Account has permission to perform an action on a resource
Did you find this article helpful?
If so, consider buying me a coffee over at 