
If you are not familiar with the oc command, refer to OpenShift - Getting Started with the oc command.
There are different ways to configure a container with environment variables.
- In a deployment YAML file
- Using Config Map
- Using Secrets (this article)
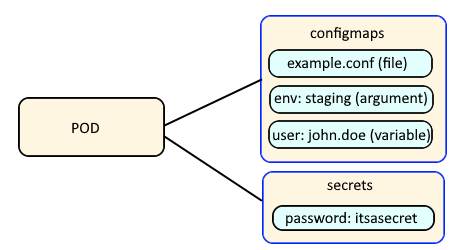
Config Maps are used to:
- mount configuration files in a container
- create environment variables in a container
- create command line option arguments in a container
Secrets are similar, used to create variables that contain encoded data (e.g. passwords). In this way, if a change is needed to a configuration file, variable, or command line option argument, you just need to update the config map or secret as opposed to having to make the change to your applications or deployments.
Let's say you create a secret named "mysecret" that contains the key "foo" and value "bar".
oc create secret generic mysecret --from-literal=foo="bar"
The oc get secrets command should show that the secret exists.
~]$ oc get secrets
NAME TYPE DATA AGE
mysecret Opaque 1 3m11s
The --output yaml or --output json options can be used to display the YAML or JSON details of the secret. Notice that the "foo" key contains "YmFy" instead of "bar". This is normal, because the secret value is base64 encoded.
~]$ oc get secrets mysecret --output yaml
apiVersion: v1
data:
foo: YmFy
kind: Secret
metadata:
creationTimestamp: "2021-11-18T07:12:09Z"
name: mysecret
namespace: default
resourceVersion: "448072461"
uid: 4104a646-84e2-46c3-bd59-408e2f7ee807
type: Opaque
On a Linux system, the base64 command can be used to decode the value.
~]# echo YmFy | base64 --decode
bar
Or, as a one line, jsonpath and base64 command can be used to decode the value.
~]# oc get secret mysecret --output jsonpath="{.data.foo}" | base64 --decode
bar
If the secret contains one or more public certificates and/or private keys, here is an example of how the public certificate details could be displayed using the oc get secret and base64 and openssl commands.
~]$ oc get secrets foo-tls --output jsonpath='{.data.tls\.crt}' | base64 --decode | openssl x509 -noout -text
Certificate:
Data:
Version: 3 (0x2)
Serial Number: 1234567891234567890 (0x1a2b3c4d5e6f7g8h)
Signature Algorithm: sha256WithRSAEncryption
Issuer: CN=openshift-service-serving-signer@1602707828
Validity
Not Before: Jan 12 20:43:07 2024 GMT
Not After : Mar 12 20:43:08 2026 GMT
Subject: CN=openshift-service-serving-signer@1602707828
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
Did you find this article helpful?
If so, consider buying me a coffee over at 