
If you are not familiar with the oc command, refer to OpenShift - Getting Started with the oc command.
Role Bindings are a way to map subjects (user, group, service account) to a Role or Cluster Role, so that the subjects have permission to perform certain actions (e.g. create, delete) on certain resources (e.g. deployments, secrets). In other words, Role Bindings are a way to apply Role Based Access Control (RBAC). Here is an illustration of how subjects (user, group, service account) get mapped to permissions. There are a number of different ways to design this, typically based on your organizations needs.
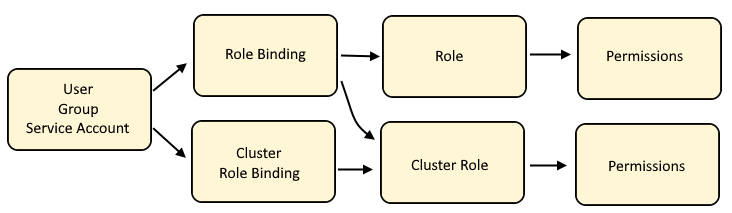
Cluster Role Binding maps a user, group or service account to a Cluster Role which will have policies that allow certain actions (such as create or delete or list) on certain resources (such as deployments, pods)
Role Bindings maps a user, group or service account to a Role or to a Cluster Role which will have policies that allow certain actions (such as create or delete or list) on certain resources (such as deployments, pods)
Cluster Role is often used by a number of different users, groups and service accounts in various projects, thus a Cluster Role contains the default actions (such as list, get, watch) on certain resources (such as deployments, pods) that users, groups, or service accounts are allowed to do across namespaces.
Role if isolated to a user, group or service account in a specific project, as a way of granting specific actions (such as create and delete and update) on certain resources (such as services and routes).
The oc get roles command can be used to list the roles that have been created in your currently selected project.
~]$ oc get roles
NAME CREATED AT
my-role 2023-01-05T08:19:22Z
The oc get clusterroles command can be used to list the roles that are automatically included with OpenShift and any additional Cluster Roles that have been created.
~]$ oc get clusterroles
NAME CREATED AT
admin 2021-07-16T17:15:10Z
my-cluster-role 2023-01-05T08:19:22Z
basic-user 2021-07-16T17:15:10Z
cluster-admin 2021-07-16T17:15:10Z
cluster-reader 2021-07-16T17:15:10Z
cluster-status 2021-07-16T17:15:10Z
edit 2021-07-16T17:15:10Z
self-provisioner 2021-07-16T17:15:10Z
view 2021-07-16T17:15:10Z
The oc describe role and oc describe clusterrole commands can be used to display the permissions granted for the cluster role or role.
~]$ oc describe role my-role
Name: my-role
Labels: <none>
Annotations: <none>
PolicyRule:
Resources Non-Resource URLs Resource Names Verbs
--------- ----------------- -------------- -----
pods [] [] [get list watch]
Role Bindings and Security Context Constraint are similar in that they both are access control mechanisms.
- Role Bindings are used to allow users, groups and service accounts certain actions (such as create or delete or list) on certain resources (such as deployments, pods)
- Security Context Constraints are used to control what pods are allowed to do
The oc adm policy command can be used to:
- Add or Remove a Role Binding or Cluster Role Binding from a User, Group or Service Account
- Add or Remove a Security Context Constraint from a User, Group or Service Account
The oc get rolebindings and oc get clusterrolebindings commands can be used to:
- List the Users, Groups, and Service Accounts that have been appended to a Role Binding or Cluster Role Binding
- List the custom Role Bindings and Cluster Role Bindings that have been created
TIP
The -A or --all-namespaces flag can be used to list the Role Bindings in every namespace.
The -n or --namespace flag can be used to list the Role Bindings in a certain namespace.
In this example, one or more Users, Groups or Service Accounts have been appended to the default basic-user Role Binding.
The Role Bindings that begin with my-role are custom Role Bindings that have been created. Check out my article on using the oc create rolebinding or oc create clusterrolebinding to create a custom Role Binding.
Notice also there is a basic-user-0 Role Binding. When you add the first User, Group or Service Account to one of the system Role Bindings using the oc adm policy command, this will create the Role Binding in the currently selected namespace (basic-user in this example). If you then added a second User, Group or Service Account to the same Role Binding oc adm policy command and you do not use the --rolebinding-name option, this will create another Role Binding with -0 appended (basic-user-0 in this example).
~]$ oc get rolebindings
NAME ROLE AGE
basic-user ClusterRole/basic-user 8d
basic-user-0 ClusterRole/basic-user 8d
my-role-admins ClusterRole/admin 10d
my-role-cluster-admins ClusterRole/cluster-admin 10d
my-role-cluster-status ClusterRole/cluster-status 10d
my-role-cluster-readers ClusterRole/cluster-reader 10d
my-role-editors ClusterRole/edit 10d
my-role-self-provisioners ClusterRole/self-provisioner 10d
my-role-viewers ClusterRole/view 10d
The oc get clusterrolebindings command can be used to list the Cluster Role Bindings that have been created.
~]$ oc get clusterrolebindings
NAME ROLE AGE
basic-users ClusterRole/basic-user 10d
cluster-admins ClusterRole/cluster-admin 10d
view ClusterRole/view 10d
You will probably want to next determine if a User, Group or Service Account has permission to perform an action on a resource to determine the subjects (User, Group, Service Account) that are bound to the Role Binding or Cluster Role Binding.
Did you find this article helpful?
If so, consider buying me a coffee over at 