
If you are not familiar with the oc command, refer to OpenShift - Getting Started with the oc command.
- Using an OpenShift route (this is the most common)
- Using an ingress route
- Using a load balancer service
- Assign an external IP address to a service
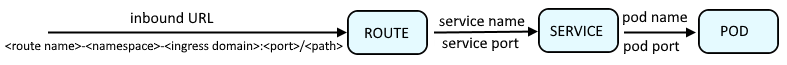
An OpenShift route or an Ingress route will provide a URL such as http://my-route-my-project.apps.openshift.example.com:8080 which is used to route a request onto a service, which is then routed onto a pod, and then to the container in the pod, and finally to the application running in the container.
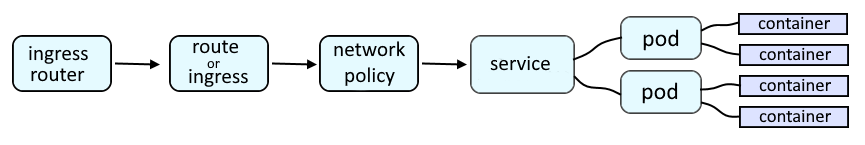
Like this.
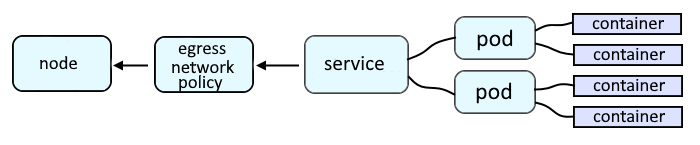
Egress provides a way for an application deployed on OpenShift to access an external URL, such as http://www.example.com.
The oc get services command can be used to list the services that have been created in a project. Let's say you want to create an Ingress route that will be used to route requests to foo-service.
~]$ oc get services
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
foo-service ClusterIP 172.30.232.182 <none> 8080/TCP,8443/TCP,8778/TCP 177d
bar-service ClusterIP 172.30.179.246 <none> 8080/TCP,8443/TCP,8778/TCP 240d
The oc create ingress command can be used to create an Ingress route that will be used to route requests onto a service.
- The syntax of --rule is <url><path>=<service>:<port> (for example - my-ingress-route.apps.openshift.example.com/my-endpoint=foo-service:8080).
- If the * (wildcard) character is NOT used in --rule, the pathType of the ingress route will be Exact and an OpenShift route will NOT be created.
- If the * (wildcard) character is used in --rule, the pathType of the ingress route will be Prefix and an OpenShift route will be created. In this scenario, if the ingress route is not annotated with termination, the route will be set as an insecured route, not using SSL or TLS termination. --annotation can be included to set the OpenShift route as an edge, passthrough, or reencrypt route.
~]$ oc create ingress my-ingress-route --rule my-ingress-route.apps.openshift.example.com/my-endpoint*=foo-service:8080 --default-backend foo-service:8080 --annotation route.openshift.io/termination=edge
ingress.networking.k8s.io/my-ingress-route created
Optionally, the tls option can be used to create an ingress route that uses HTTPS. In this scenario, you would first need to create a secret that contains the appropriate public certificate and private key that can be used by the route.
~]# oc create secret tls my-tls-secret --cert tls.crt --key tls.key
secret/my-tls-secret created
And then create the ingress route, including tls=<secret name>.
~]$ oc create ingress my-ingress-tls-route --rule my-ingress-route.apps.openshift.example.com/my-tls-endpoint*=foo-service:8443,tls=my-tls-secret --default-backend foo-service:8443 --annotation route.openshift.io/termination=edge
ingress.networking.k8s.io/my-ingress-route created
The oc get ingress command can then be used the list the Ingress routes in the currently selected project.
~]$ oc get ingress
NAME CLASS HOSTS ADDRESS PORTS AGE
my-ingress-route <none> my-ingress-route.apps.openshift.example.com 80 15m
my-ingress-tls-route <none> my-ingress-tls-route.apps.openshift.example.com 80, 443 15m
The oc get ingress command with the --output yaml option can be used to show the YAML for each ingress route.
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: my-ingress-route
namespace: my-project
annotations:
route.openshift.io/termination: passthrough
spec:
defaultBackend:
service:
name: my-service
port:
number: 8080
rules:
- host: my-ingress-route.apps.openshift.example.com
http:
paths:
- backend:
service:
name: my-service
port:
number: 8080
path: /my-endpoint
pathType: Prefix
status:
loadBalancer: {}
I'm not sure why, but I have to label the route to get the route exposed on the default router
oc label ingress my-ingress-route route-type=default
And curl can be used to submit a request to the ingress route, which should forward the request onto the service, and then onto the pod.
curl -v http://my-ingress-route.apps.openshift.example.com/my-endpoint
Did you find this article helpful?
If so, consider buying me a coffee over at 