
If you are not familiar with the oc command, refer to OpenShift - Getting Started with the oc command.
Role Bindings are a way to map subjects (user, group, service account) to a Role or Cluster Role, so that the subjects have permission to perform certain actions (e.g. create, delete) on certain resources (e.g. deployments, secrets). In other words, Role Bindings are a way to apply Role Based Access Control (RBAC). Here is an illustration of how subjects (user, group, service account) get mapped to permissions. There are a number of different ways to design this, typically based on your organizations needs.
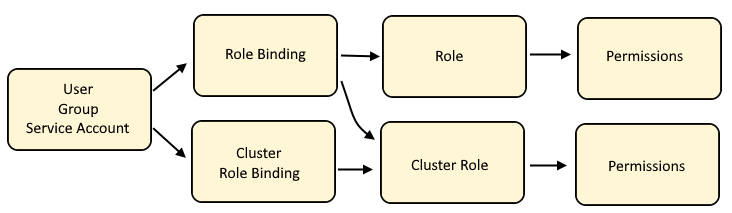
Cluster Role Binding maps a user, group or service account to a Cluster Role which will have policies that allow certain actions (such as create or delete or list) on certain resources (such as deployments, pods)
Role Bindings maps a user, group or service account to a Role or to a Cluster Role which will have policies that allow certain actions (such as create or delete or list) on certain resources (such as deployments, pods)
Cluster Role is often used by a number of different users, groups and service accounts in various projects, thus a Cluster Role contains the default actions (such as list, get, watch) on certain resources (such as deployments, pods) that users, groups, or service accounts are allowed to do across namespaces.
Role if isolated to a user, group or service account in a specific project, as a way of granting specific actions (such as create and delete and update) on certain resources (such as services and routes).
The oc describe role and oc describe clusterrole commands can be used to list the permissions of what is allowed with a Role or Cluster Role.
~]$ oc describe role my-role
Name: my-role
PolicyRule:
Resources Non-Resource URLs Resource Names Verbs
--------- ----------------- -------------- -----
pods [] [] [get list watch]
Role Bindings and Security Context Constraint are similar in that they both are access control mechanisms.
- Role Bindings are used to allow users, groups and service accounts certain actions (such as create or delete or list) on certain resources (such as deployments, pods)
- Security Context Constraints are used to control what pods are allowed to do
The oc adm policy command can be used to:
- Add or Remove a Role Binding from a User, Group or Service Account (this article)
- Add or Remove a Security Context Constraint from a User, Group or Service Account
The oc create rolebinding or oc create clusterrolebinding commands can be used to create a custom Role Binding instead of using one of the 8 default Role Bindings.
AVOID TROUBLE
Let's say there is already a basic-user Role Binding. If you don't use the --rolebinding-name option, then a new Role Binding such as basic-user-0 will be created. The --rolebinding-name option is used to append additional Users, Groups, or Service Accounts to the Role Binding if it already exists.
If you have not yet created a Role Binding or Cluster Role Binding, check out my article FreeKB - OpenShift - Create Role Binding.
Roles and Cluster Roles
Before creating a Role Binding or Cluster Role Binding that maps to a Cluster Role, the oc get clusterrole command can be used to determine if the Cluster Role exists.
~]$ oc get clusterrole cluster-admin
NAME CREATED AT
cluster-admin 2023-07-07T15:30:54
Or in the OpenShift console at User Management > Roles, you can search for the Cluster Role.
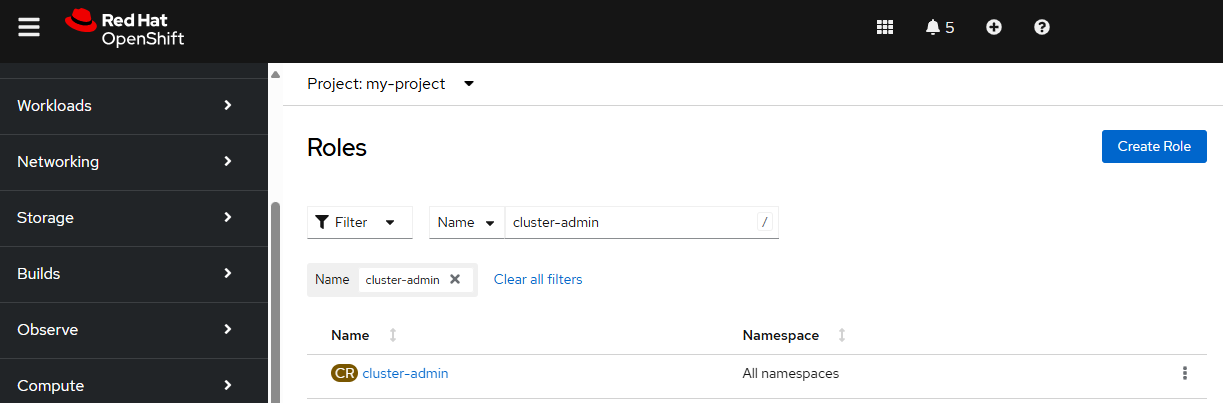
If the Cluster Role does not exist, you can create the Cluster Role. Check out my article FreeKB - OpenShift - Create Roles.
oc create clusetrrole my-cluster-role --verb get --verb list --verb watch --resource pods
Similarly, before creating a Role Binding that maps to a Role (not a Cluster Role), the oc get role command can be used to determine if the Role exists.
~]$ oc get role my-role --namespace my-project
NAME CREATED AT
my-role 2025-06-18T01:23:03Z
Or in the OpenShift console at User Management > Roles, you can search for the Role.
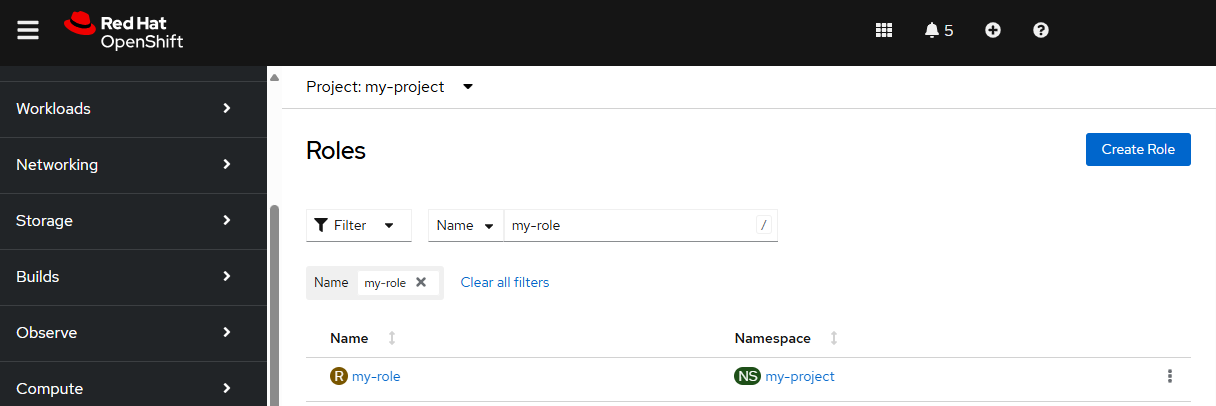
If the Role does not exist, you can create the Role. Check out my article FreeKB - OpenShift - Create Roles.
oc create role my-role --verb get --verb list --verb watch --resource pods --namespace my-project
Determine if a User, Group or Service Account has permission to perform an action on a resource
Before Adding or Removing a Role Binding or Cluster Role Binding from a subject (User, Group, Service Account) you will probably want to first determine if a User, Group or Service Account has permission to perform an action on a resource
Add Role Binding to User, Group or Service Account
add-role-to-user can be used to create or update a Role Binding, to associate a user or service account with the Role Binding. If the -z option is not used, the Role Binding will be created or updated to associate a user with the Role Binding.
- If the Role Binding does not exist, the Role Binding will be created
- If the Role Binding already exists, the Role Binding will be updated
oc adm policy add-role-to-user my-role john.doe --rolebinding-name my-role-binding --role-namespace my-project --namespace my-project
The -z option can be used to create or update a Role Binding to associate a service account with the Role Binding.
oc adm policy add-role-to-user my-role -z my-service-account --rolebinding-name my-role-binding --role-namespace my-project --namespace my-project
add-role-to-group can be used to create or update a Role Binding, to associate a group with the Role Binding.
- If the Role Binding does not exist, the Role Binding will be created
- If the Role Binding already exists, the Role Binding will be updated
oc adm policy add-role-to-group my-role my-group --rolebinding-name my-role-binding --role-namespace my-project --namespace my-project
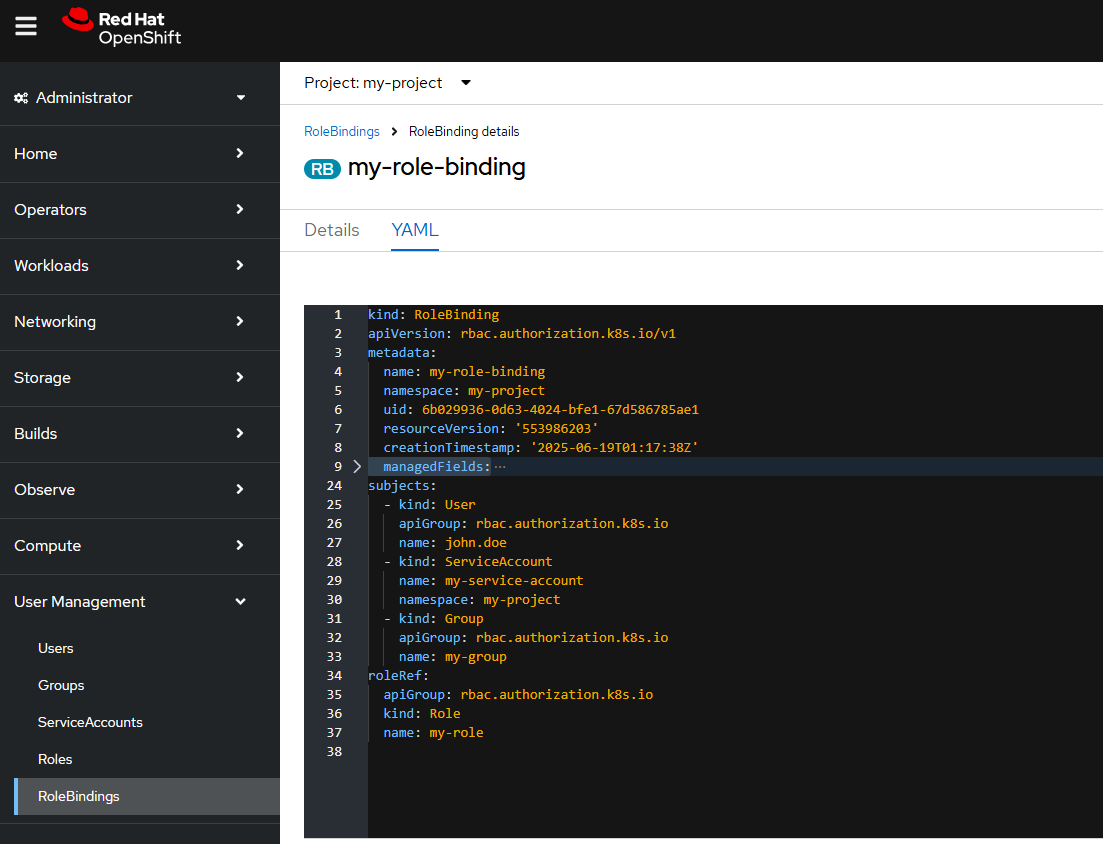
Or you can edit the Role Binding YAML, updating subjects.
kind: RoleBinding
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: my-role-binding
namespace: my-project
uid: 40771e90-0774-4531-93a4-67279aa89582
resourceVersion: '553981432'
creationTimestamp: '2025-06-19T01:10:22Z'
subjects:
- kind: User
apiGroup: rbac.authorization.k8s.io
name: john.doe
- kind: ServiceAccount
name: my-service-account
namespace: my-project
- kind: Group
apiGroup: rbac.authorization.k8s.io
name: my-group
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: my-role
Or in the OpenShift console, in the Administrator view, at User Management > RoleBindings, you can edit the Role Binding YAML, updating subjects.
Add Cluster Role Binding to User, Group or Service Account
add-cluster-role-to-user can be used to create or update a Cluster Role Binding, to associate a user or service account with the Cluster Role Binding. If the -z option is not used, the Cluster Role Binding will be created or updated to associate a user with the Cluster Role Binding.
- If the Cluster Role Binding does not exist, the Cluster Role Binding will be created
- If the Cluster Role Binding already exists, the Cluster Role Binding will be updated
Be aware that if you do not include the --rolebinding-name command line option, a new Cluster Role Binding will be created, named <role name>-<lowest unused integer>. In this example, if there is not already a Cluster Role Binding named basic-user-0, then the new Cluster Role Binding would be basic-user-0. If Cluster Role Binding basic-user-0 already exists, then the Cluster Role Binding would be basic-user-1. Basically, the new Cluster Role Binding will be the role name (basic-user in this example) and the lowest unused integer. The --rolebinding-name option can be used to create a Cluster Role Binding with a specific name.
The --rolebinding-name option must be included if you want to update a certain Cluster Role Binding. If you do not include the --rolebinding-name option, then a new Cluster Role Binding will be created.
oc adm policy add-cluster-role-to-user basic-user john.doe --rolebinding-name my-cluster-role-binding
The -z option can be used to create or update a Cluster Role Binding to associate a service account with the Cluster Role Binding.
oc adm policy add-cluster-role-to-user basic-user -z my-service-account --rolebinding-name my-cluster-role-binding
add-cluster-role-to-group can be used to create or update a Cluster Role Binding, to associate a group with the Cluster Role Binding.
- If the Cluster Role Binding does not exist, the Cluster Role Binding will be created
- If the Cluster Role Binding already exists, the Cluster Role Binding will be updated
oc adm policy add-cluster-role-to-group basic-user my-group --rolebinding-name my-cluster-role-binding
Remove User, Group or Service Account from a Role Binding
Let's say Role Binding my-role-binding contains three subjects, user john.doe, group my-group, and service account my-service-account.
~]$ oc get rolebinding my-role-binding --namespace my-project --output yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
creationTimestamp: "2025-06-19T01:48:53Z"
name: my-role-binding
namespace: my-project
resourceVersion: "554005200"
uid: 11245b42-e37c-4596-a038-bbc5550ae580
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: my-role
subjects:
- apiGroup: rbac.authorization.k8s.io
kind: User
name: john.doe
- kind: ServiceAccount
name: my-service-account
namespace: my-project
- apiGroup: rbac.authorization.k8s.io
kind: Group
name: my-group
remove-role-from-user can be used to remove a user from a Role Binding.
oc adm policy remove-role-from-user my-role john.doe --rolebinding-name my-role-binding --role-namespace my-project --namespace my-project
The -z option can be used to remove a Service Account from a Role Binding.
oc adm policy remove-role-from-user my-role -z my-service-account --rolebinding-name my-role-binding --role-namespace my-project --namespace my-project
remove-role-from-group can be used to remove a group from a Role Binding.
oc adm policy remove-role-from-group my-role my-group --rolebinding-name my-role-binding --role-namespace my-project --namespace my-project
Remove User, Group or Service Account from a Cluster Role Binding
remove-cluster-role-from-user can be used to remove a user from a Cluster Role Binding.
oc adm policy remove-cluster-role-from-user my-cluster-role john.doe --rolebinding-name my-cluster-role-binding
The -z option can be used to remove a Service Account from a Cluster Role Binding.
oc adm policy remove-cluster-role-from-user my-cluster-role -z my-service-account --rolebinding-name my-cluster-role-binding
remove-cluster-role-from-group can be used to remove a group from a Cluster Role Binding.
oc adm policy remove-cluster-role-from-group my-cluster-role my-group --rolebinding-name my-cluster-role-binding
Did you find this article helpful?
If so, consider buying me a coffee over at 