
There are multiple different types of Identity Providers (IdP) that OpenShift can use for authentication.
- htpasswd
- kubeadmin
- LDAP sync (Active Directory)
- Red Hat build of the Keycloak Operator
- Red Hat Single Sign-On (SSO)
Both the Red Hat build of the Keycloak Operator and Red Hat Single Sign-On (SSO) (this article) use keycloak as the backend Identity Provider (IdP) system. Red Hat Single Sign-On (SSO) is much easier to install and configure but may limit you from being able to use or configure certain features. For example, Red Hat Single Sign-On (SSO) installs and configures a Postgres SQL database for you, whereas with Red Hat build of the Keycloak Operator you install and configure the Postgres SQL database.
This assumes you have already
- Installed the Red Hat Single Sign On (SSO) Operator
- Setup keycloak resource for Red Hat Single Sign On (SSO)
- You can sign into the Red Hat Single Sign On (SSO) console
Create a Realm
In the left panel of the Red Hat Single Sign On (SSO) console, hover over the realm namespace (which by default is Master) and select Add realm.
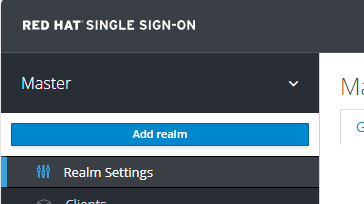
Create a new realm.
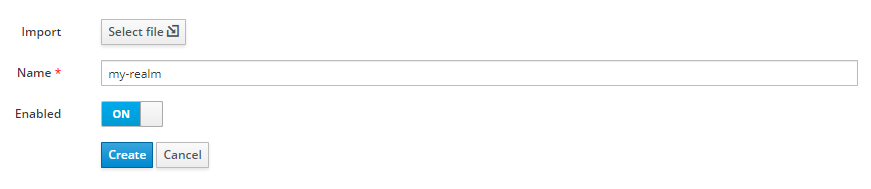
Create a User
Select Users > Add user.
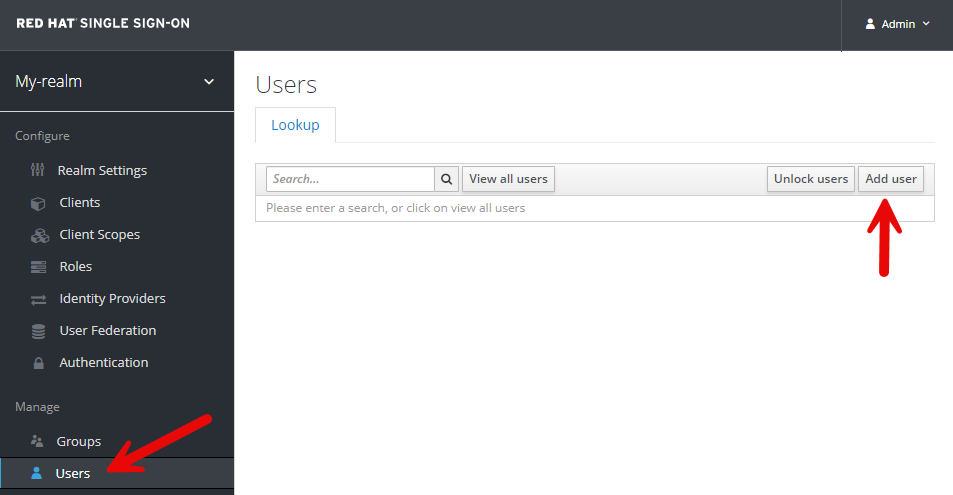
Create the users account.
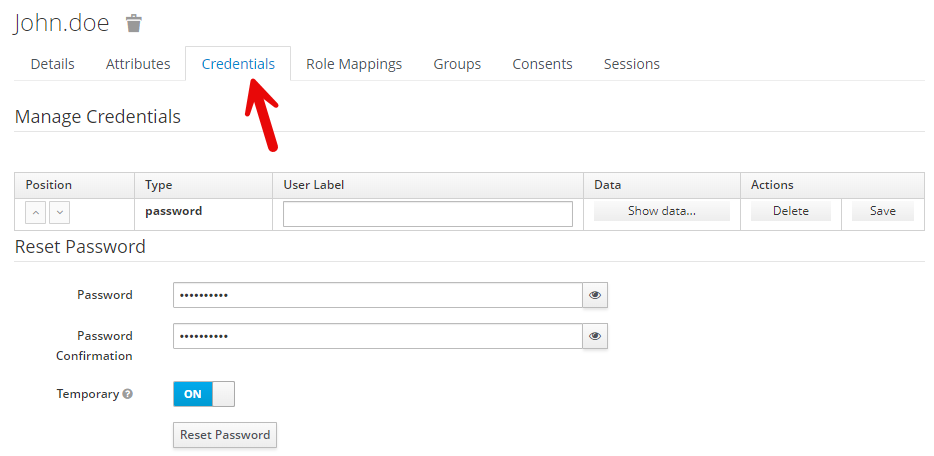
Select the Credentials tab and give the user a password.
Create OpenID Connect Client
Next you will probably want to create a Red Hat Single Sign On (SSO) OpenID Connect Identity Provider.
Did you find this article helpful?
If so, consider buying me a coffee over at 